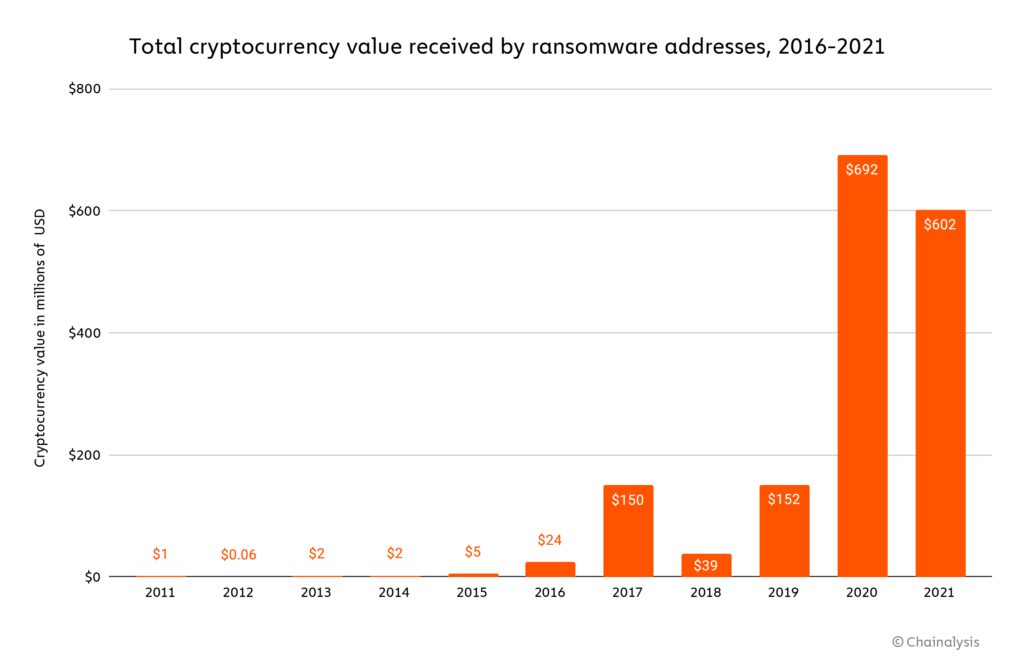
A new report estimates that ransomware payments tallied at least $602 million in 2021 — but the actual total could be much higher.
Blockchain analysis firm Chainalysis released new data on Feb. 10 about ransomware activity related to cryptocurrency in 2021. However it stated that the total value is likely to end up surpassing the $692 million taken in 2020.
“In fact, despite these numbers, anecdotal evidence, plus the fact that ransomware revenue in the first half of 2021 exceeded that of the first half of 2020, suggests to us that 2021 will eventually be revealed to have been an even bigger year for ransomware.”
The average ransomware payment size reached a record high of $118,000 in 2021. This is a 26% increase from the average of $88,000 in 2020. Chainalysis attributes the larger average payment size to a “big game hunting” strategy increasingly employed by ransomware strains in which large organizations are targeted for ransomware.
Last year also had the highest amount of active ransomware strains than any other year on records. At least 140 strains received crypto payments, which is 21 more than in 2020 and 61 more than in 2019.
Conti was the most active ransomware strain in 2021. It siphoned off nearly $200 million in value through cryptocurrency in 2021. Conti, thought to be based in Russia, is a ransomware syndicate that sells its program as a service to affiliates for a fee.
Darkside came in a distant second to Conti by extracting nearly $100 million in crypto value. Darkside is the organization that held the Colonial Pipeline hostage last year, and demanded ransom be paid in Bitcoin (BTC).

Although the report states that most ransomware strains come and go in waves, staying active for a short amount of time before becoming dormant, Conti was active throughout the entirety of 2021. More commonly, ransomware groups will halt operations then reopen under a new name.
The trend to rebrand caused the average strain in 2021 to last for only 60 days, which is 2.8 times lower than in 2020, when the average was 168 days.
Related: Google Cloud to detect crypto-mining malware on virtual machines
Chainalysis concluded that while most ransomware attacks are financially motivated, others appear to have geopolitical goals focused on “deception, espionage, reputational damage and disruption of the enemy government’s operations.”
It pointed out that although there are benefits to utilizing cryptocurrency to execute ransomware attacks, the transparency of crypto transactions makes it easier for authorities to track the movement of funds. North Korea has repeatedly used crypto to circumvent economic sanctions for years.