North Korean hackers are posing as excellent candidates in recruitment drives. This is so they are employed in Web3 companies. Once in, they can steal all of the digital assets of the companies that hire them. Neil Dundon of Cryptorecruit explains how it works.
Our experience recruiting in the crypto sphere has taken a rather weird turn when it comes to North Korean hackers. We are at the coalface of this issue. It is strange to be dealing with it every day.
North Korean Hackers
This behavior was first noticed by Cryptorecruit back in early 2020. Although, it may have been going on longer. This was a time when the crypto markets were charging into full bull mode. Recruiting in the space was blasting off at unprecedented levels.
Alas! When we hired a new consultant to work with us, that consultant would often tell us about a super strong candidate they came across. I would immediately recognize it as a fake. This was always much to the new consultant’s dismay!
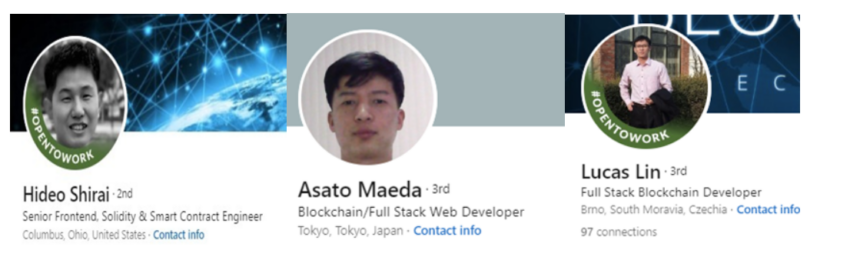
It takes a little bit of time to work out the back story to these profiles. But then it clicks. On every single fake profile, there are always tell-tale signs that things aren’t as legit as they seem.
We aren’t making wild uneducated guesses here. We have thoroughly tested such profiles. The language they use is exactly the same in every case – like they are reading from a script. We can only assume they are operating out of a call center somewhere. Most likely, it is based in the depths of North Korea.
Tell Tale Signs
The first red flag is the profile picture. It is the ultimate giveaway. Recruiters just have a look at the shot. The sparkling applicant often claims to be Japanese. But, you quickly realize that they are not at all Japanese. And then there is the vacuous look in their eyes. Like they are robots, or at least generated by an AI tool. They surely have no soul.
It is very unusual to see a phone number. But if there is a phone number included, it’s a U.S. number. They can be coaxed onto a call with you. But it’s usually on Skype. And if you do actually connect, you have to utterly insist they turn their camera on. When you get them in view, they don’t look like real people. They actually look like robots. It’s very unsettling and strange!
North Korean Hackers and the jobs they want
So what are the jobs these operatives apply for? Usually, they say they are a Solidity developer, blockchain developer, or something Web3-related.
Their LinkedIn profiles always use a very familiar and identifiable template. These templates are full of the most beautiful keywords. These are words that recruiters and employers in the crypto space could only hope to see on a good day.
When recruiters post a job ad, you can be sure that these fake profiles will immediately auto-reply to it. But here’s the truth. Any Solidity developer worth their salt is not actually applying for positions. In fact, they are getting targeted by recruiters all the time. They have multiple opportunities on the go.
These hackers applying for jobs is probably the biggest red flag. If their profile looks fanatstic, and they have years of Solidity experience, then be careful. Of course, there can be exceptions to the rule. But stay on guard.
North Korean Hackers: What are their motivations?
The motivation for these nefarious individuals is to get paid in crypto, and then hack defi protocols. It can take months for management to figure out that a developer is a dud. By this stage, they’ve probably been paid $30,000 or more. And worse, had access to many of the company’s internal systems. They have possibly built relationships with other employees and could have had an opportunity to coerce them.
Multiply this by the hundreds, or even thousands of fake profiles to get the real picture. Kim Jong Un is certainly bringing in some pretty decent revenue. It will fund his nuke program rather nicely.
My personal opinion is that employers hiring these candidates directly led to major hacks across the crypto space. In fact, the $600m Axie infinity hack was attributed to North Korean hackers without dispute.
You can protect yourself. Watch out for red flags mentioned here. Be suspicious. Ultimately, a candidate needs to prove who they are. And, what they can do.
If you’re still not sure, contact me with their Linkedin profile. My team and I are all over it.
About the author

Neil Dundon is the founder of Cryptorecruit and has over 15 years of experience specializing in recruitment. Cryptorecruit has been in the crypto space since early 2016. CryptoRecruit understands what drives sentiment within space, whether that be developers’ motivations for shifting course within blockchain companies, or your average Wall Street executive looking to enter the space.
Got something to say about North Korean hackers or anything else? Write to us or join the discussion in our Telegram channel. You can also catch us on Tik Tok, Facebook, or Twitter.
Disclaimer
All the information contained on our website is published in good faith and for general information purposes only. Any action the reader takes upon the information found on our website is strictly at their own risk.


